Today we are going to take a look at how to self host Bitwarden on a Raspberry Pi.
Before we look at how to set up Bitwarden on a Raspberry Pi, I want to make sure that I highlight that we will be installing Bitwarden RS. (now, Vaultwarden). Vaultwarden is an unofficial version of Bitwarden that’s great for self-hosting.
Overall, if you’re interested in self-hosting the open source password manager Bitwarden, this is what I consider to be the best option. There are two prerequisites that must be installed (Docker/Portainer, Nginx Proxy Manager). I will link to tutorials in the instructions if you haven’t set those up yet.
To have this exposed outside of your local network, you will need a domain name. If you haven’t purchased one, you can use a free DuckDNS domain name which we will configure in later steps.
Following the instructions below to Self Host Bitwarden on a Raspberry Pi will work on any device running Docker and Portainer (not only Raspberry Pi’s running Raspbian OS).
1. Self Host Bitwarden on a Raspberry Pi
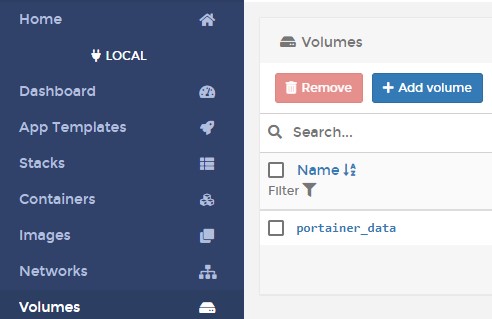
1. Ensure that you have Docker and Portainer installed on your Raspberry Pi. Technically, you don’t have to install Portainer, but I find it easier to manage my Docker containers that way, so I’ll be using that to install Bitwarden on a Raspberry Pi.
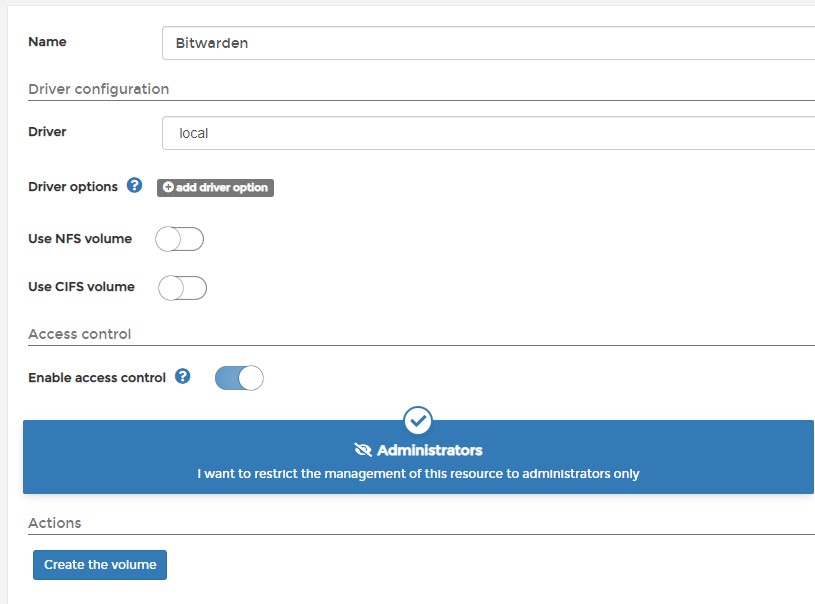
2. Select Volumes then Add Volume.
3. Add a Name, then Create the volume. This is where all of your important information will be stored, so back up this folder if you’d like to ensure your data is backed up.
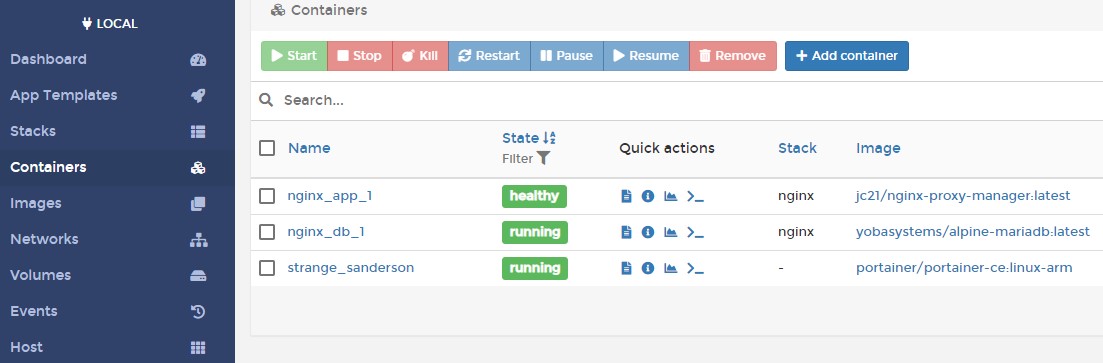
4. Select Containers then Add Container.
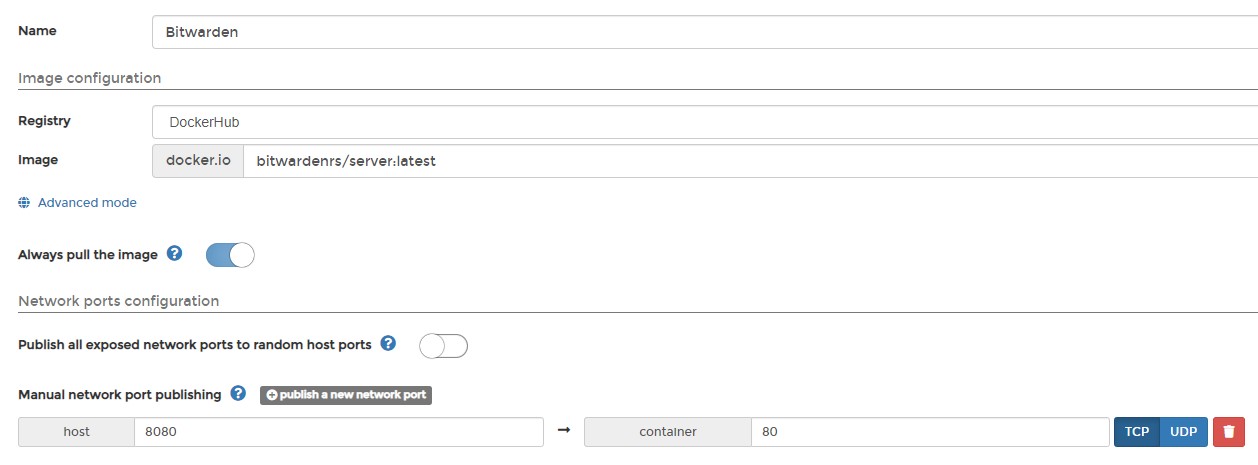
5/3/21 Update: The bitwardenrs image has been deprecated and renamed to vaultwarden. For this reason, you will have to use that image name (as opposed to what the screenshot is showing).
5. Give the container a Name, then in the Image section, add vaultwarden/server:latest so docker pulls the latest image. Finally, publish a new network port and map the host port 8080 to the container port 80.
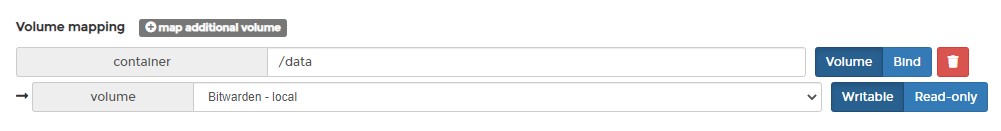
6. Select Volumes, then map the /data container path to the Bitwarden volume we created earlier.
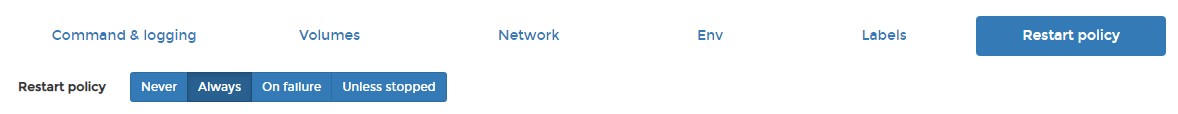
7. Change the Restart Policy to Always, then Deploy the container.
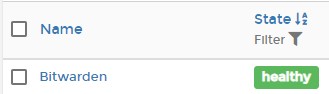
8. Give the container a few minutes, and it should be healthy.
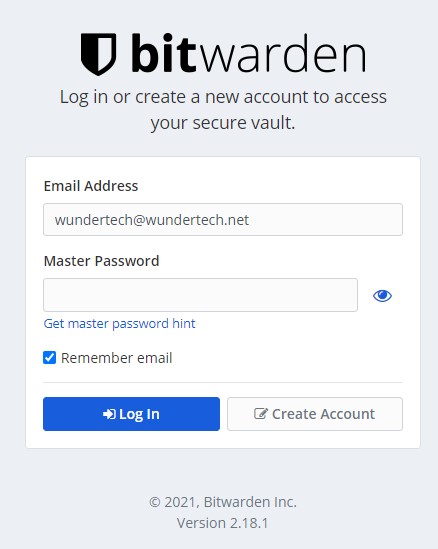
9. Connect to the IP address of your Raspberry Pi and Port 8080 to access the web interface. This is to confirm that everything is loading as expected on the bitwarden server.
http://[RASPBERRY_PI_IP:8080
1.1 Reverse Proxy Setup
The recommended approach for exposing Bitwarden outside of your local network is by using a reverse proxy. In this tutorial, I will be using Nginx Proxy Manager which will be hosted on the same Raspberry Pi.
If you’d like to use Nginx Proxy Manager, you can learn how to set it up here. Alternatively, you do not have to use Nginx Proxy Manager, or a reverse proxy server hosted on your Raspberry Pi. You can use a separate reverse proxy server if you’d like.
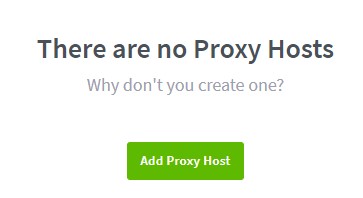
1. Select Proxy Hosts, then Add Proxy Host.
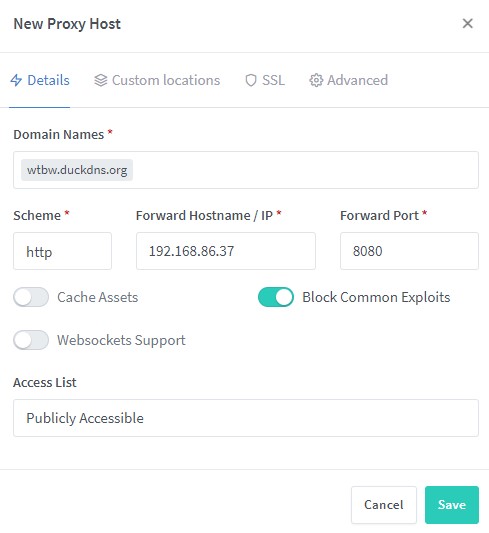
2. Enter in the Domain Name you’d like to use. Leave the scheme as http, enter in the IP address of your Raspberry Pi and port 8080. Select Block Common Exploits and Save.
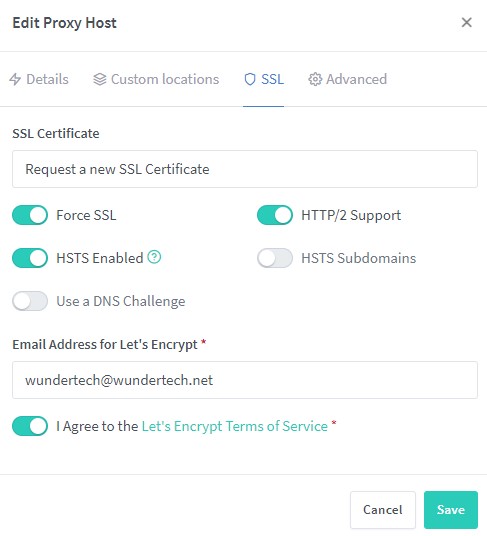
3. Edit the record we just created, select SSL, then Request a new SSL Certificate. Make sure you enable Force SSL, HTTP/2 Support, and HSTS Enabled. Agree to the terms and Save. The SSL certificate will now be retrieved.
4. When you click the domain name, you will now be brought to the login page for Bitwarden! Create your account so that you can log in.
1.2 Disable Account Creations
After you’ve created your account, you can disable account creation if you’d like. To do so, stop the Bitwarden container.
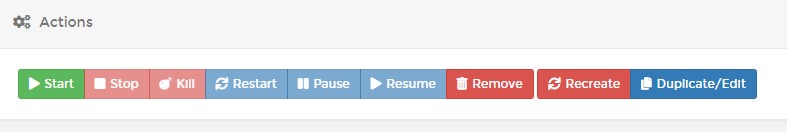
1. Inside of the container, select Duplicate/Edit.
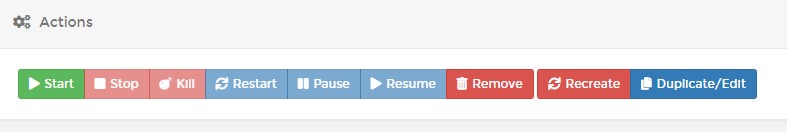
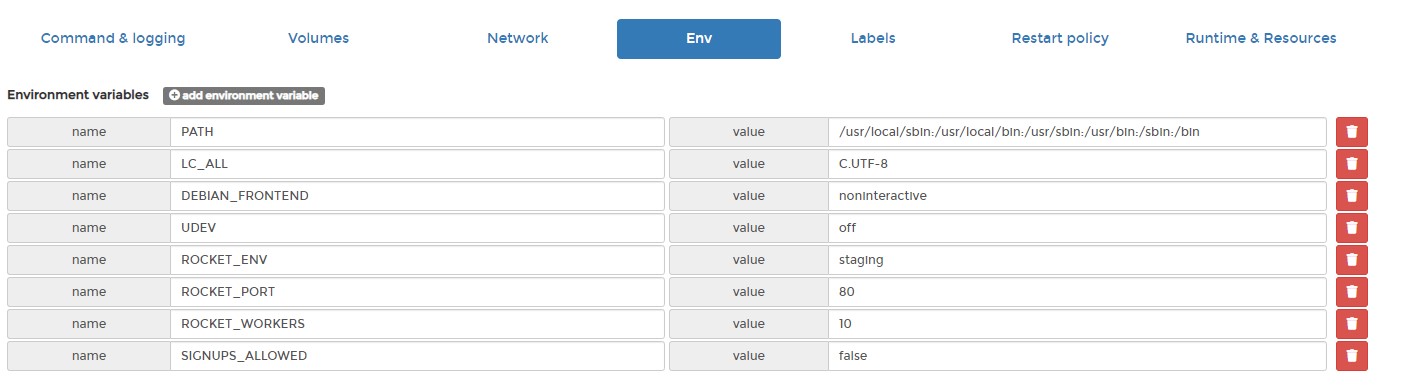
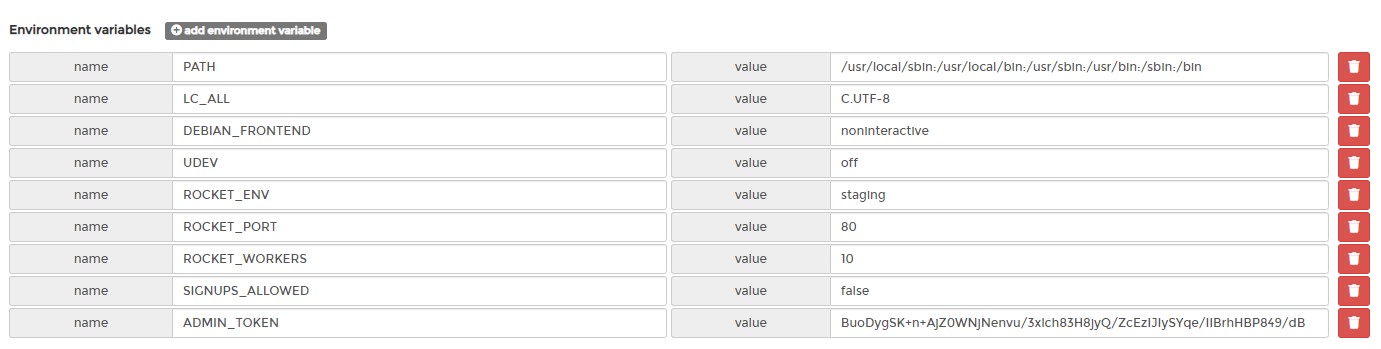
2. Add an environment variable named SIGNUPS_ALLOWED with the value false. Then, Deploy the container. When you get a popup stating that a container already exists under that name, Replace it.
3. If you now try and create a new account, you will no longer be able to. However, the account you already created will still exist!
1.3 Enabling Admin Page
There are various things that you can do with the admin page of Bitwarden RS if you’d like. You can learn about some of those options here. Follow the instructions below to enable the admin page.
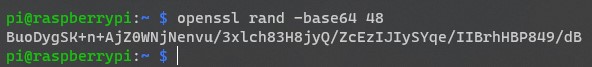
1. From the command-line of your Raspberry Pi, enter the command below. In my opinion, it’s easiest to do this from a separate PC so that you can SSH in and copy the string.
openssl rand -base64 48
2. This will create a random string that is 48 characters long. Copy that string and save it.
3. Stop the container. Inside of the container, select Duplicate/Edit.
4. Add an environment variable named ADMIN_TOKEN, then add the 48-character string that you created in the last step.
Then, Deploy the container. When you get a popup stating that a container already exists under that name, Replace it. Make sure that you save this 48 character string since you will need it to access the admin page.
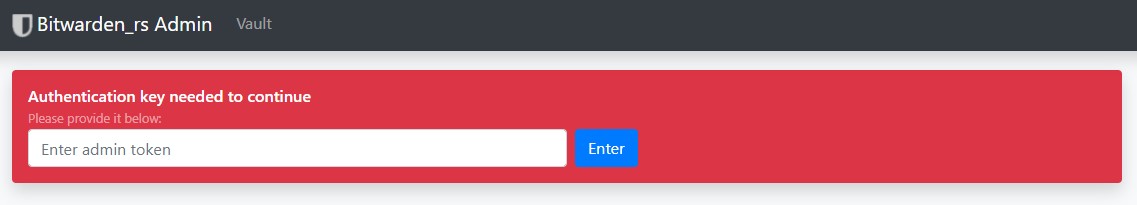
5. The admin page will now be accessible by the domain name you’re using and /admin. You can access the admin settings by entering in that 48 character string.
https://[YOUR_DOMAIN_NAME]/admin
2. Conclusion – Self Host Bitwarden on a Raspberry Pi
This tutorial looked at how to self host Bitwarden on a Raspberry Pi! Bitwarden on a Raspberry Pi is awesome, and Bitwarden (VaultWarden) is a great alternative that will allow you to self-host the password manager.
Make sure that you are always using two-factor authentication for your account. This cannot be stated enough.
Thanks a lot for checking out the tutorial on how to self host Bitwarden on a Raspberry Pi. As always, if you have any questions on how to self host Bitwarden on a Raspberry Pi, please leave a comment in the YouTube video above!