In this article, we will look at Tailscale vs. WireGuard to determine which is the best VPN option to use.
Before we look at Tailscale vs. WireGuard, it’s important to understand that these are both applications that will allow you to configure a VPN. A VPN will allow you to connect to the location where your VPN server is located and access devices, or simply secure your connection by creating a secure tunnel back to the VPN server.
VPNs are used extensively in personal and business environments and are generally viewed as the safest and most secure way to access a secondary device or network.
Please check out some of our Tailscale or WireGuard tutorials if you’re interested in setting up either!
Tailscale vs. WireGuard: Which VPN Server is Best for You?
The main difference between Tailscale and WireGuard is that WireGuard is a self-hosted VPN server, while Tailscale adds user authentication and device management to the WireGuard VPN Protocol. Tailscale also relies on cloud servers for authentication and connection, while WireGuard is fully self-hosted and only relies on your private server.
Before looking at Tailscale vs. WireGuard more in-depth below, I want to explain exactly what they both are and how they function.
What is Tailscale?
Tailscale is a VPN service that utilizes the WireGuard Protocol. Tailscale allows you to easily create a VPN tunnel with absolutely no port forwarding. For users who have a CGNAT or simply do not feel comfortable port forwarding, Tailscale is one of the easiest ways to configure a VPN tunnel.
It’s also important to know that while Tailscale utilizes the WireGuard Protocol, it does not function the same way that WireGuard does. While they utilize the exact same point-to-point encryption, using Tailscale requires the Tailscale network to be accessible.
This means that if Tailscale experiences an outage, you will not be able to use your VPN.
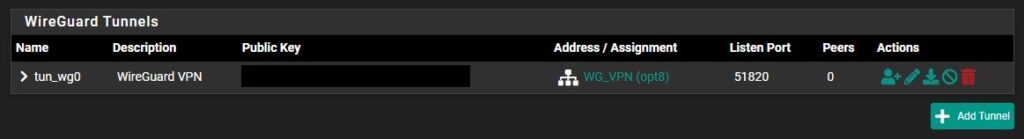
What is WireGuard?
WireGuard is a VPN tool that’s faster, simpler, and leaner than something like OpenVPN. Where OpenVPN has the benefit of longevity, WireGuard is the newer, faster VPN protocol that many people are looking to try and it’s supported on various platforms.
While Tailscale utilizes the WireGuard protocol, it relies on the Tailscale servers. WireGuard only relies on the server that it’s hosted on, meaning that if the server is online and accessible, the VPN tunnel is technically online. When comparing this to Tailscale, the device must be online and the Tailscale servers must be accessible.
Performance Differences Between Tailscale and WireGuard
To get straight to the point, WireGuard is faster than Tailscale. If you look at it from a bare-minimum perspective, WireGuard and Tailscale both use the same underlying technology.
However, Tailscale builds on top of it to include user authentication and better compatibility with devices that wouldn’t traditionally support WireGuard. This is where the loss in performance comes from, as well as the additional requirement for the Tailscale server availability.
All of this leads to an overall product that’s slower than WireGuard. With that said, depending on your requirements, the overall performance may be something that you never notice and the ease-of-use enhancements that Tailscale provides may be more desirable, which we’ll look at below.
Setup Process Differences
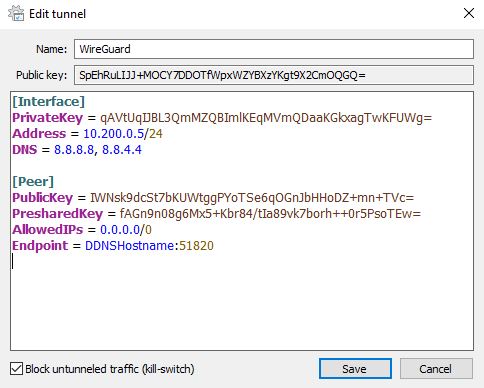
While WireGuard is faster, Tailscale is significantly easier to use. WireGuard is key based, meaning that each device will have a private key and a public key.
The public key is used to connect to a device, meaning that if you’re attempting to connect from a Windows client to a WireGuard server, the Windows client will have the WireGuard server’s public key (as the peer), and the WrieGuard server will have the Windows client’s public key (as the peer – they swap public keys).
While key-based authentication works (extremely well), it’s sometimes confusing to new users. It can also get more confusing as you add on additional security features like pre-shared keys (which must match on both devices to authenticate).
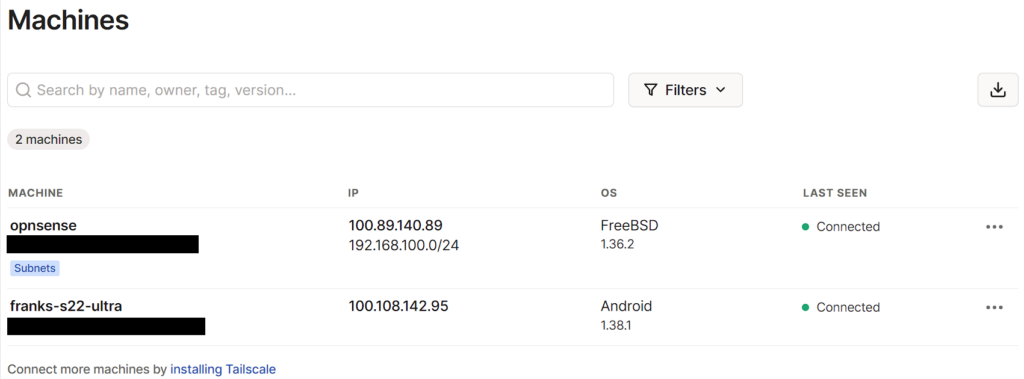
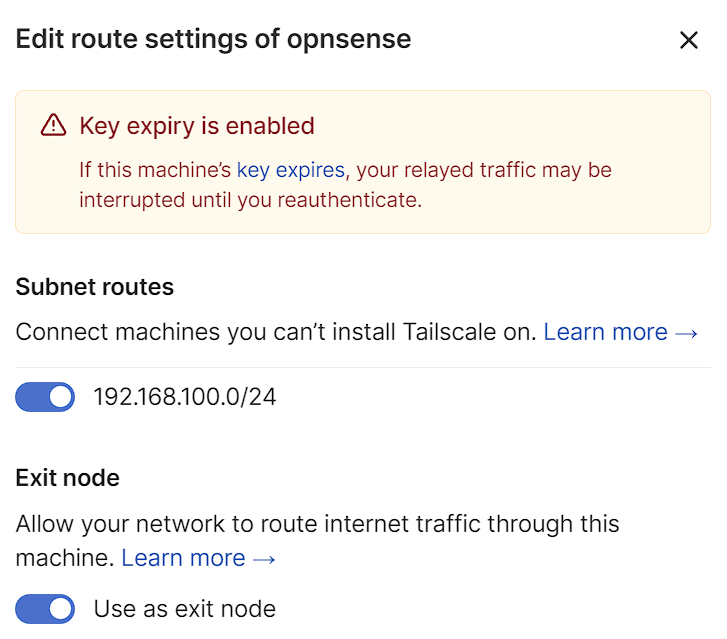
When comparing this to Tailscale, after adding a device and logging in, the device automatically appears in the Tailscale portal. From there, it’s assigned an IP address that can be used to access the device directly (when connected to the VPN).
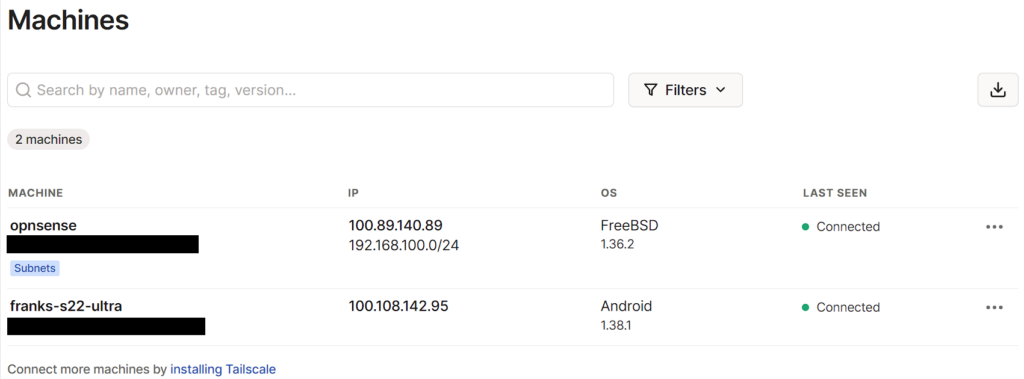
Subnets can also be defined which will allow you to access devices using their local IP address (192.168.100.0/24 above). When comparing the Tailscale authentication (username and password) with the key-based authentication that WireGuard provides, it’s crystal clear that it’s significantly easier to use and set up Tailscale.
Tailscale also gives you the same benefits as WireGuard, meaning you can set up a split-tunnel or full-tunnel VPN. A full tunnel VPN (all traffic is routed through Tailscale) is configured using an exit node.
Port Forwarding Requirement
While the initial setup for Tailscale is easier than it is for WireGuard, I also want to point out that you must port forward the selected UDP port on your router to get WireGuard to work.
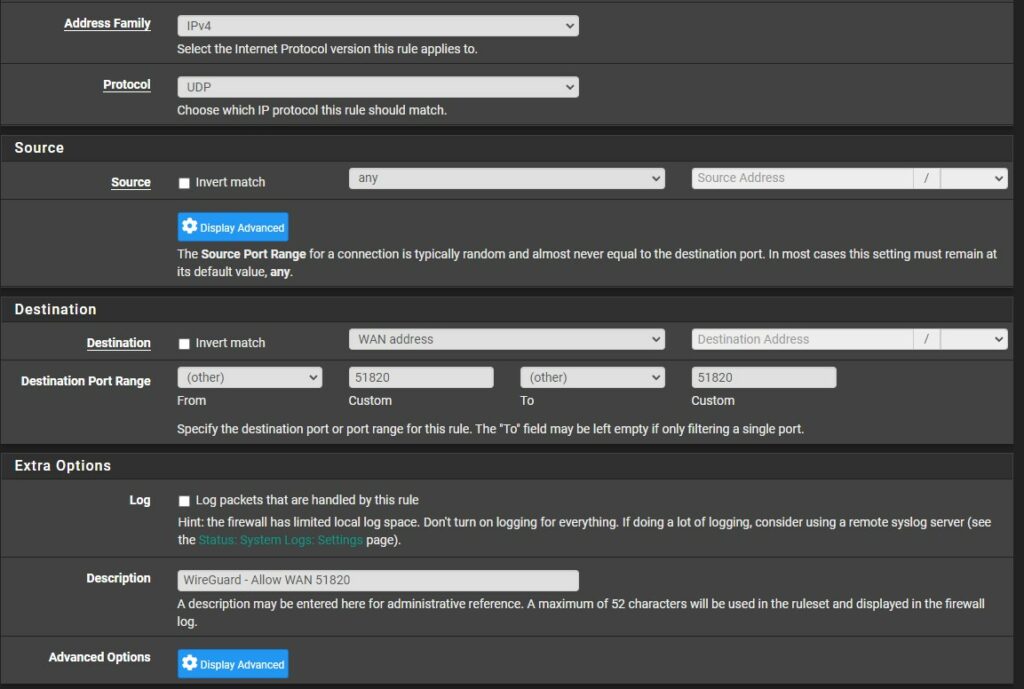
This is not a requirement for Tailscale, and while port forwarding to the WireGuard VPN port is not necessarily a security concern, there are users who cannot port forward due to ISP limitations or simply do not want to. In cases like this, WireGuard is not an option, but Tailscale will work perfectly.
Licensing Costs
While Tailscale is easier to set up, it is only free for personal users. As of the writing of this article, the free tier of Tailscale provides access to one user and 20 total devices. As soon as you’d like to give permission to other users, you must upgrade to a higher plan.
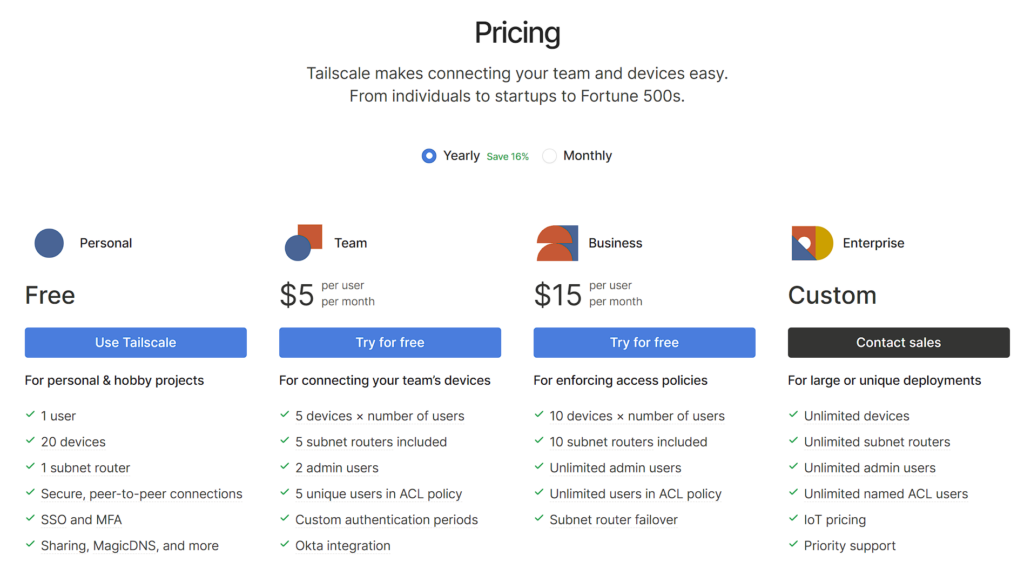
Unlike Tailscale, WireGuard is entirely free. You can have as many users as you’d like and will never be charged. This doesn’t necessarily make WireGuard better, as managing a large set of users with key-based authentication is burdensome, but it is free.
Key Differences Between Tailscale and WireGuard
This chart highlights some other key differences between Tailscale vs. WireGuard to help understand a little more what their key differences are.
| Tailscale | WireGuard | |
|---|---|---|
| Underlying Protocol | Uses WireGuard under the hood for the actual connections. | WireGuard is a VPN protocol itself. |
| Ease of Use | Zero-configuration setup by utilizing a mesh networking setup. | Requires manual setup for each peer connection. |
| Networking | Provides automatic mesh networking, allowing any device to directly reach any other regardless of their respective locations. | Provides point-to-point connections. Network topology needs to be manually configured. |
| Platform Support | Wide platform support including Windows, MacOS, Linux, iOS, Android, and more. | Native support in Linux. Third-party clients are available for other platforms. |
| Pricing | Free for personal use (up to 3 users). Paid plans for businesses. | Completely free as it’s an open-source project. |
| Security | Uses WireGuard for secure connections, adds additional features like two-factor authentication. | Offers secure point-to-point connections with strong encryption. No additional security features are built-in. |
Conclusion and Final Thoughts: Tailscale or WireGuard?
This article looked at Tailscale vs. WireGuard. While I am a big fan of Tailscale and find there to be many benefits, WireGuard is the better solution for most people. Mainly because the key-based authentication is completed once and as soon as you understand and implement it, you’ll have a faster VPN server that doesn’t rely on additional servers as Tailscale does.
While I do love WireGuard, if you cannot or do not want to port forward, Tailscale is your best option. It will do everything that WireGuard does, in an extremely similar package, with easier authentication. The downside is that if you’re not using it for personal use only (one user), you will have to upgrade your plan.
Tailscale is also a great option for users who simply do not want to manage keys with WireGuard. While it’s not particularly difficult to set up, it is a much bigger effort than Tailscale. Please check out some of our Tailscale or WireGuard tutorials if you’re interested in setting up either!
Thanks for checking out the article on Tailscale vs. WireGuard. If you have any questions, please leave them in the comments!