In this article, we will look at how to set up Tailscale on pfSense.
Tailscale is a zero-configuration VPN, which means that without any port forwarding, you’ll be able to access all the devices on your local network. Now that Tailscale is supported on pfSense, it’s a great location to run Tailscale.
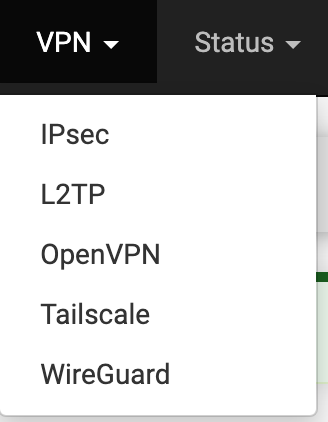
Please keep in mind that if you’d like to utilize a more traditional VPN, you can still set up OpenVPN or WireGuard. However, both of these options require port forwarding, whereas Tailscale doesn’t. From a pure configuration standpoint, Tailscale is incredibly easy to set up and we’ll look at how to set up Tailscale on pfSense below.
How to Set Up Tailscale on pfSense
Please run the steps below to set up Tailscale on pfSense.
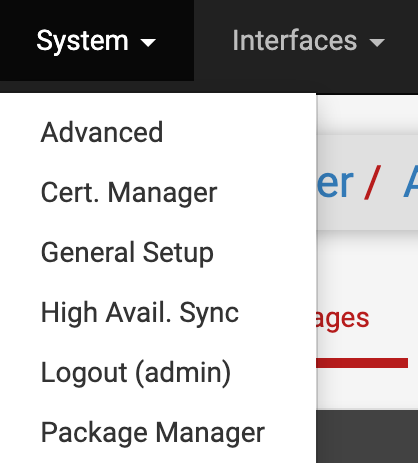
1. Select System, then Package Manager.
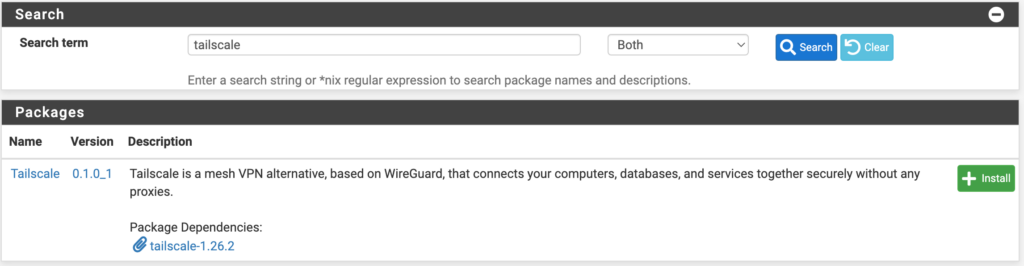
2. Search for Tailscale, then install the Tailscale package.
3. Select VPN, then Tailscale to launch the Tailscale settings.
4. At this point, we need to configure the pre-authentication key. This can be created on the Tailscale website. If you don’t already have an account, create one, then log in and select Settings, then Keys.
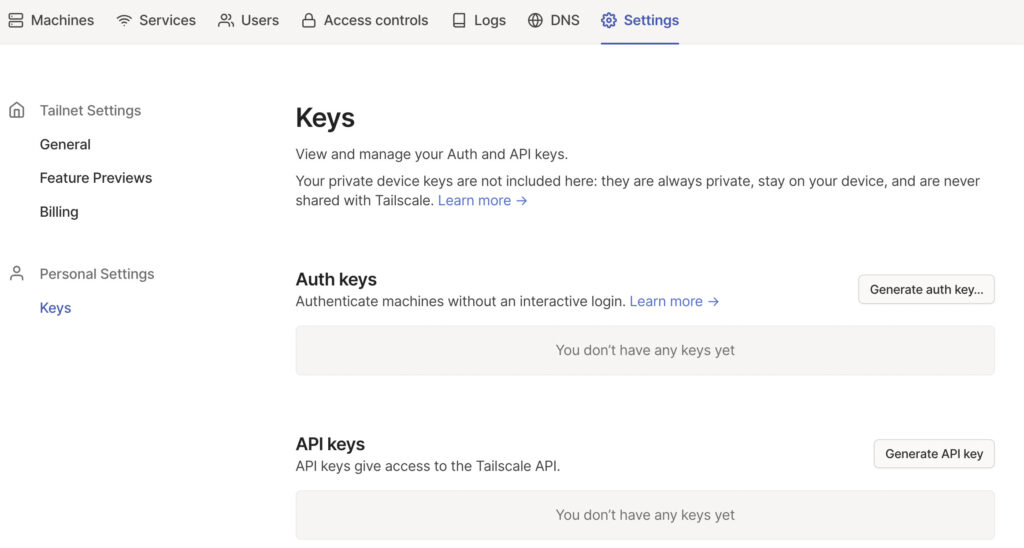
5. Select generate auth key so that we can create the key for pfSense. Select Generate Key (the settings can stay as default).
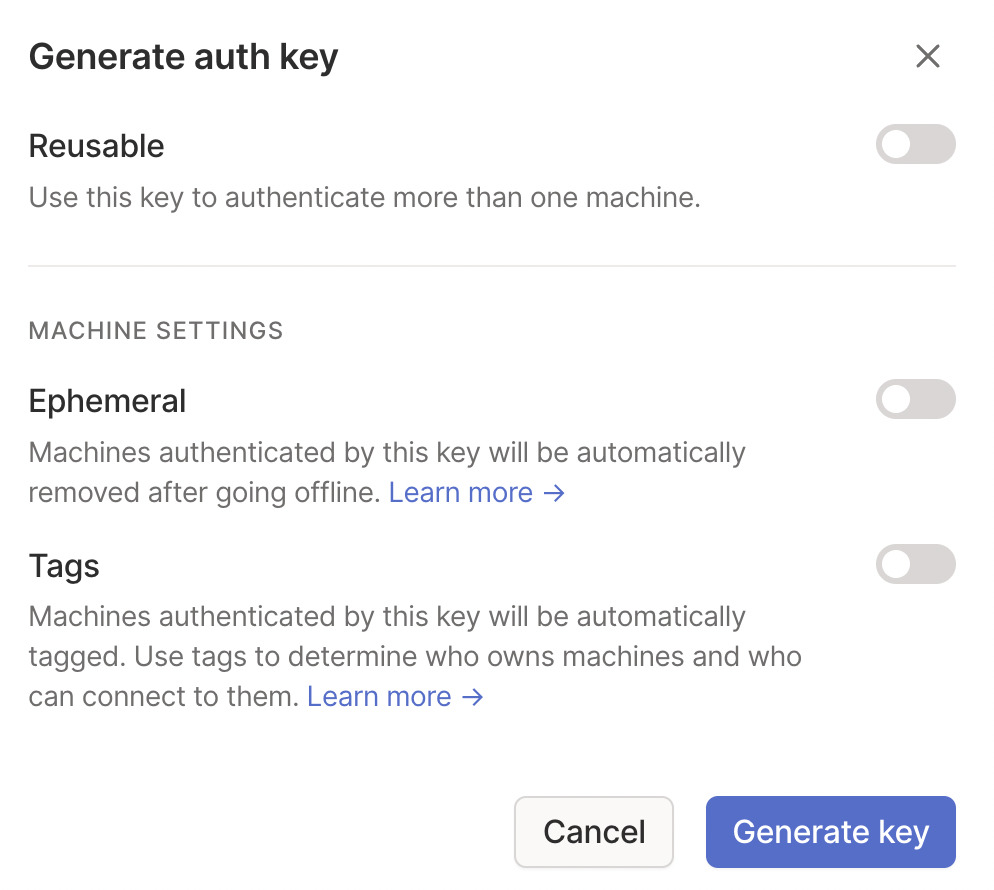
6. After the key has been generated, copy it, then go back to the Authentication section of Tailscale on pfSense.
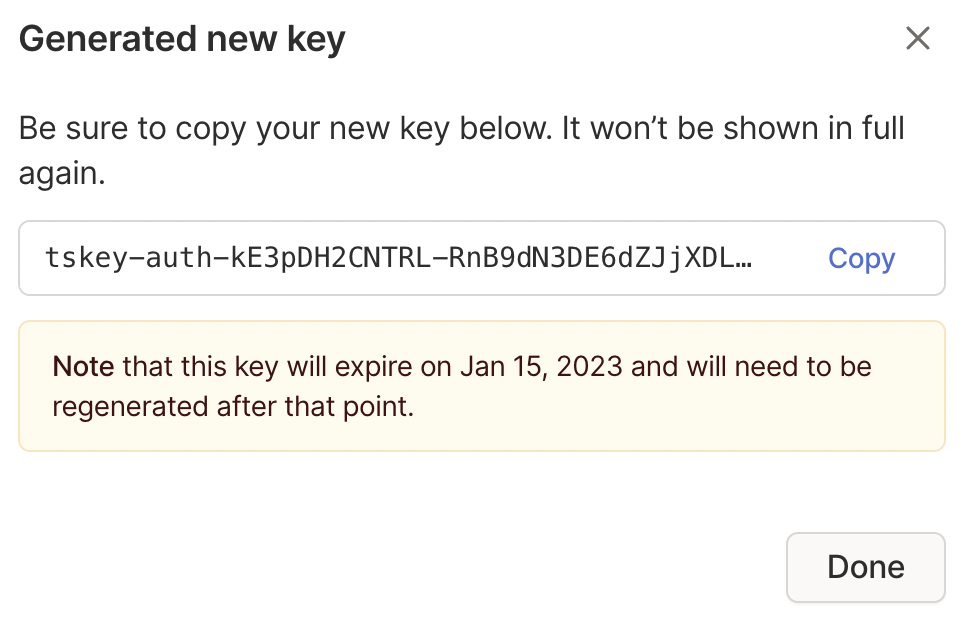
7. Paste the key that was just created, then select save.
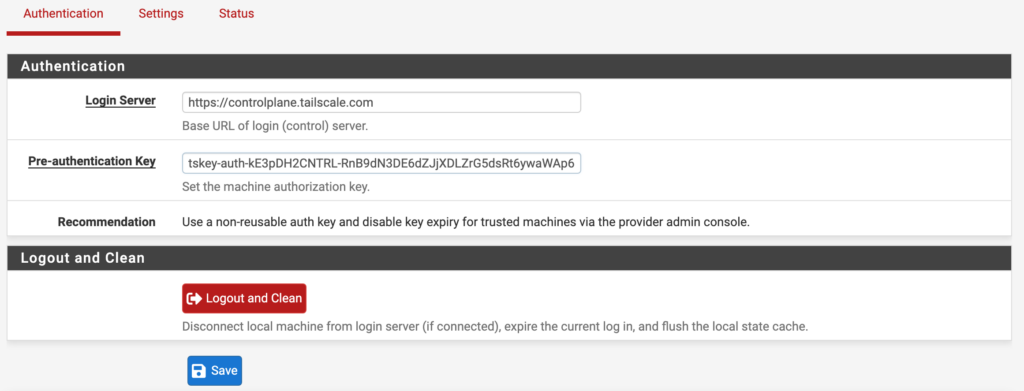
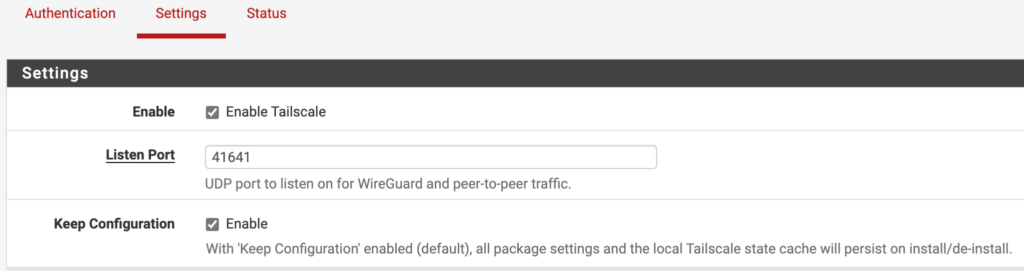
8. After saving, select Settings, then enable Tailscale and Save.
Exit Node Configuration
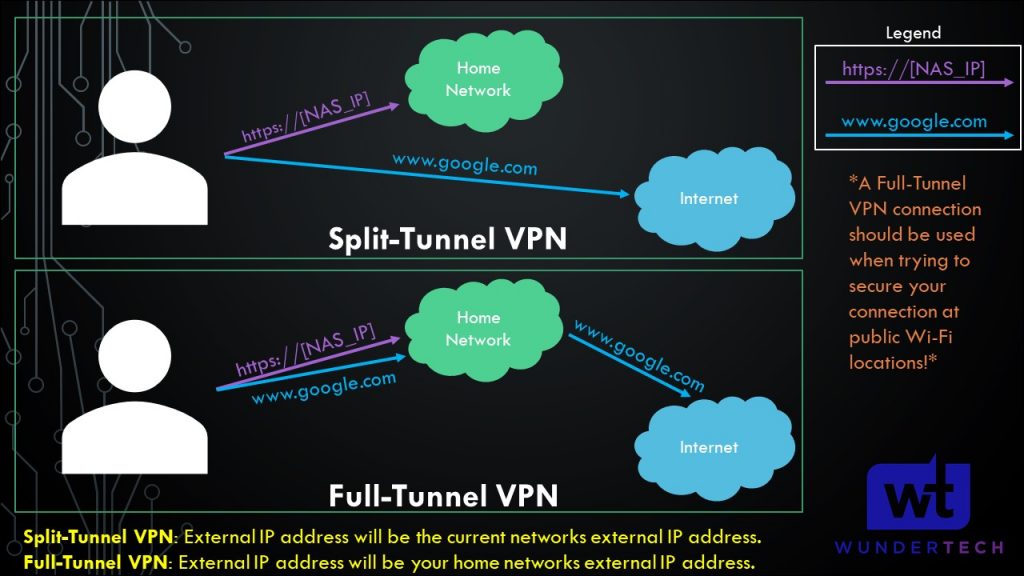
If you set up Tailscale as an Exit Node, the Exit Node can be used as a full-tunnel VPN. The image below shows what a full-tunnel vs split-tunnel VPN is, but the important point is that all traffic will be routed through Tailscale if you use an exit node. Therefore, if you’re on public Wi-Fi, it’s probably a good idea to use this feature as you’ll be tunneling all traffic through pfSense (thus, securing the connection).
A few things must be configured to set this an exit node in Tailscale:
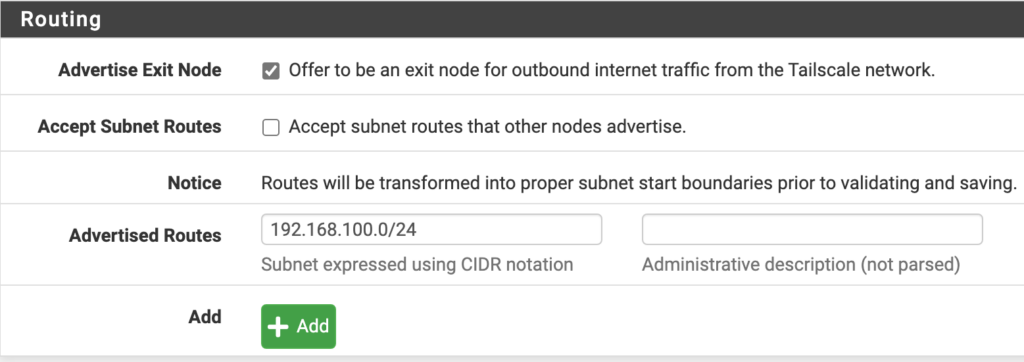
1. Inside the Tailscale settings on pfSense, enable the offer to be an exit node for outbound internet traffic from the Tailscale network option. Also, set the Advertised Routes as your local subnet (that you’d like to be able to access from external networks), then save.
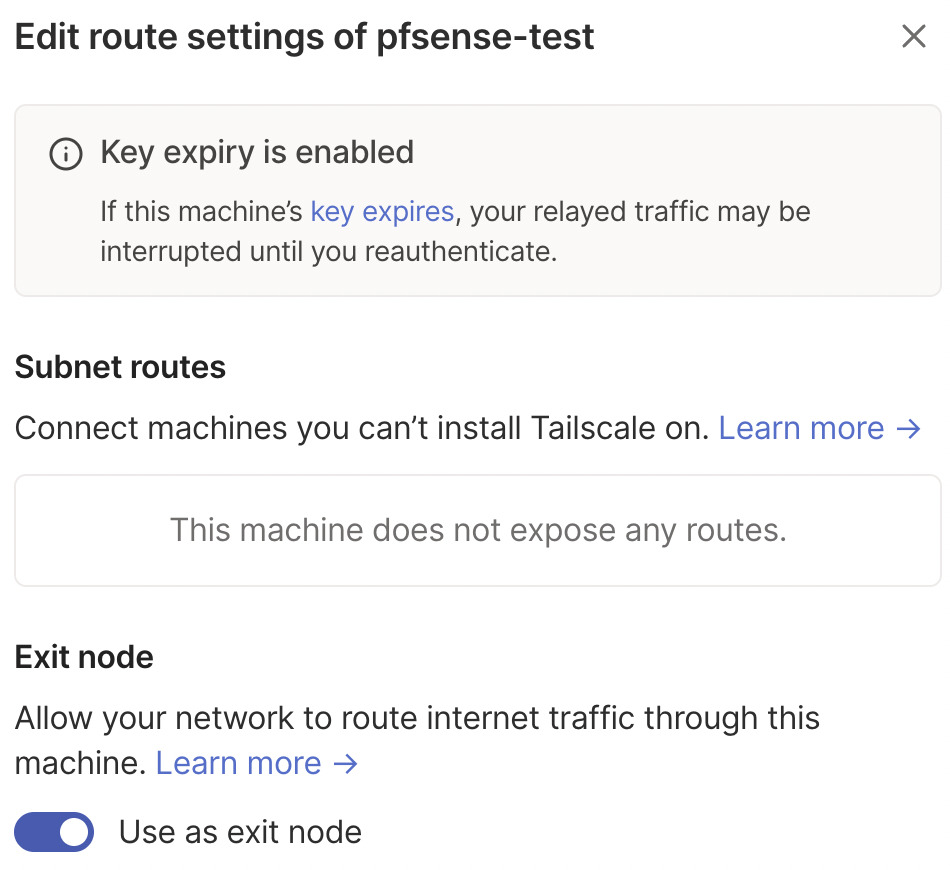
2. On the Tailscale website, select Machines, then the three ellipses next to your pfSense system, then Edit Route Settings.
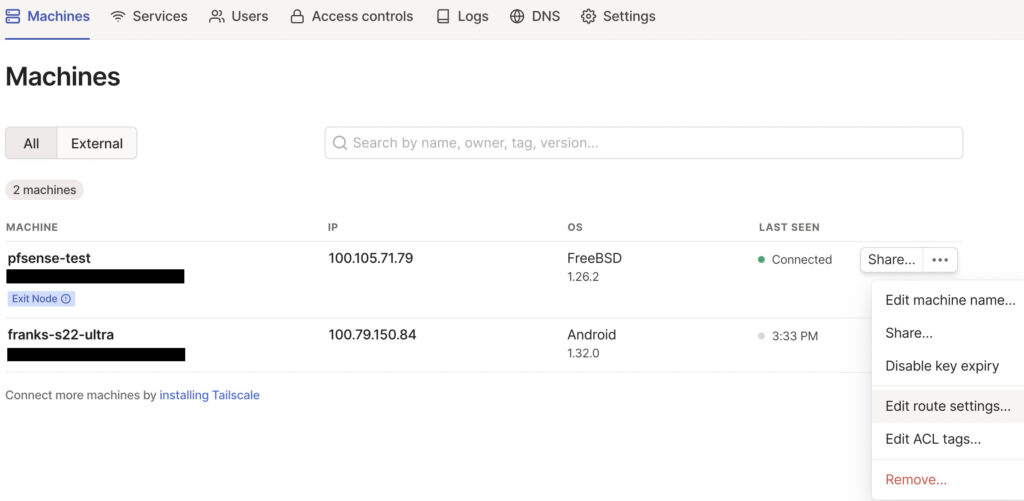
3. Select use as exit node. The exit node functionality is now set up and can be used by client devices.
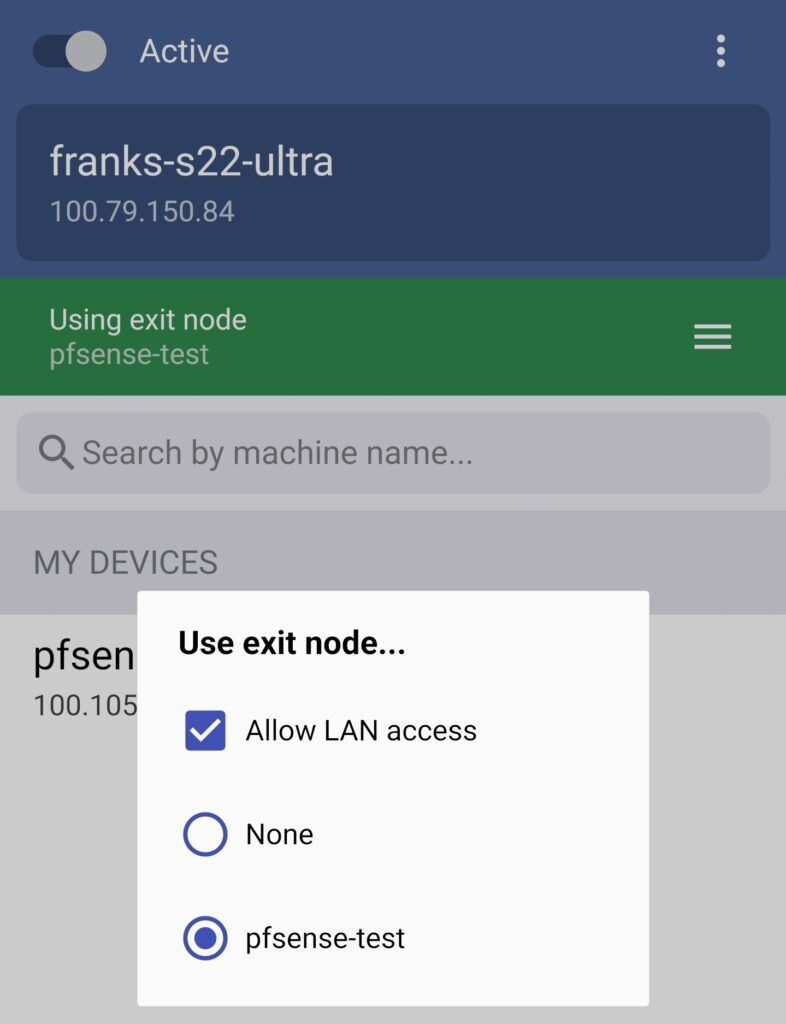
4. On whatever application you’re using, select Use Exit Node and change the exit node to be pfSense. If you do not want to use the exit node, select None, but ensure that Allow LAN Access is enabled so that you’re able to connect to your local devices.
5. Tailscale is now configured! You can now add other devices or simply connect to Tailscale from an external network to access all of your local devices.
Conclusion & Final Thoughts: Tailscale Setup Process
This tutorial looked at how to set up Tailscale on pfSense. Tailscale couldn’t possibly be easier to set up and it’s (in my opinion) the easiest and fastest way of setting up a VPN server on pfSense. It is important to note that this isn’t a traditional VPN the way that OpenVPN or WireGuard is, but it’s the fastest way to access your local network and doesn’t require any port forwarding.
Thanks for checking out the tutorial on how to set up Tailscale on pfSense. If you have any questions, please leave them in the comments!