This tutorial we will look at how to backup a Synology NAS to a Raspberry Pi using Hyper Backup.
We will first set up an Rsync server on a Raspberry Pi so that it can be used with Synology’s Hyper Backup. After completing this, you will be able to use your Raspberry Pi as an on-site or off-site backup destination. There are two sections that will guide you through the process of setting up the server. The first will show you how to format an external hard drive and install the Rsync server on your Raspberry Pi.
After the setup is complete, you should be able to see and back up your NAS to your Raspberry Pi and attached hard drive. The second section will show you how to setup your Raspberry Pi to automatically connect to your OpenVPN server when powered on.
This is incredibly helpful when using your Raspberry Pi as an offsite backup, as you can simply “power on” the Raspberry Pi and it will automatically connect to your VPN which means the backup job can start without interacting with the Raspberry Pi. Leave it at a family member or friends house and ask them to turn it on and you are good to go!
Prerequisites
1. Ensure that you have installed Raspberry Pi OS and can SSH into your Raspberry Pi.
2. If you will be completing the second portion of this tutorial for offsite backups, ensure that your OpenVPN server is setup to assign static IP addresses.
These are the two prerequisites we will need to complete to backup a Synology NAS to a Raspberry Pi.
Setup a Raspberry Pi as an Rsync Server – Backup a Synology NAS to a Raspberry Pi
1. The first step is to format your external hard drive as ext4 and make a file system. NOTE: it’s best to try and use an external hard drive that has its own power supply as you don’t want to rely on the Raspberry Pi powering your external hard drive if it isn’t absolutely necessary.
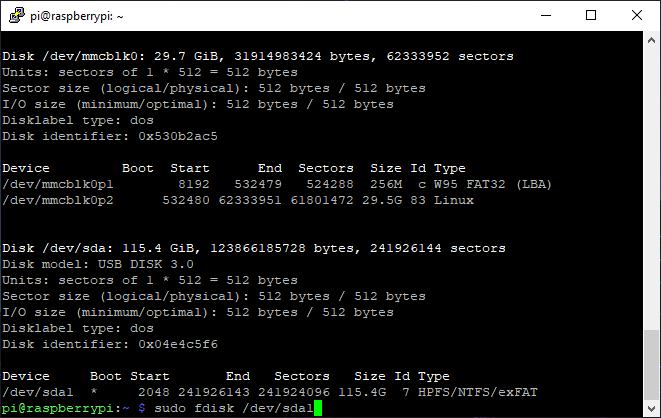
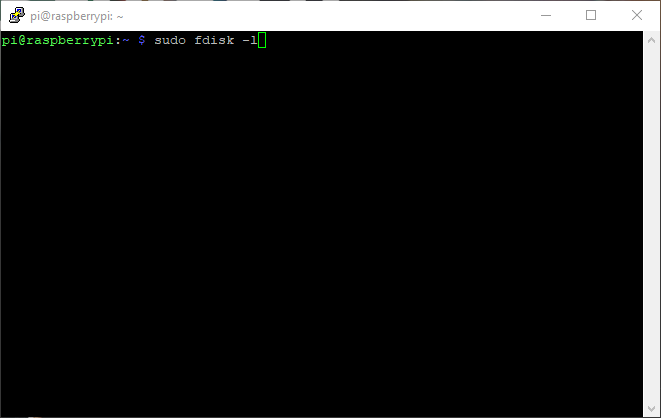
2. Run these commands to find your external hard drive, format it, and make a file system.
sudo fdisk -l sudo fdisk /dev/sda1
NOTE: Ensure that you are using the path of your external hard drive.
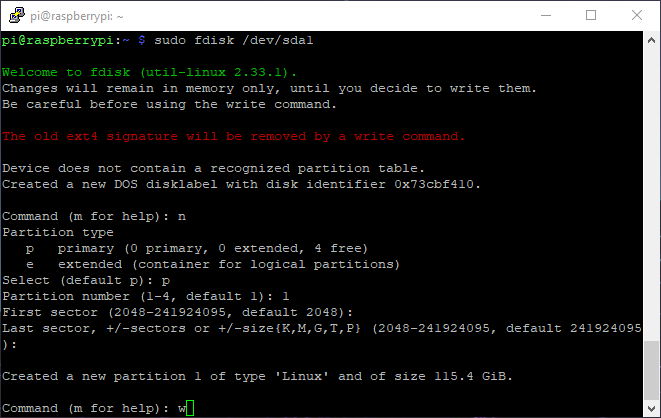
2. Type “n” to create a new file system and use all the default values by pressing “enter”, until the last step where you will need to press “w” to write.
3. Reboot the system.
sudo reboot now
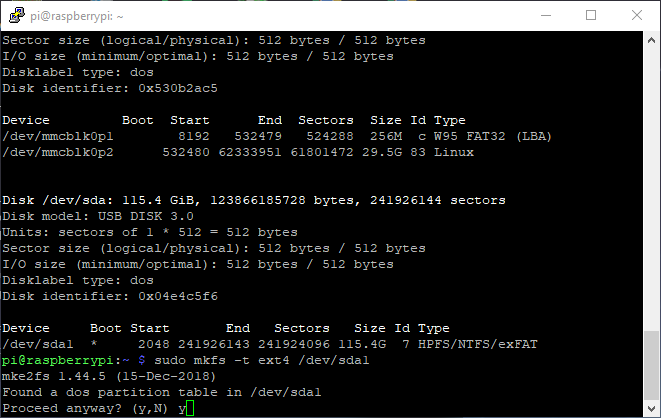
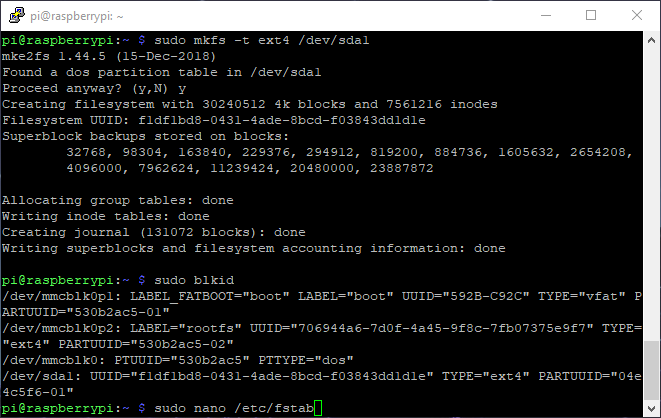
4. Ensure that your external hard drive has the same path as earlier and make a file system.
sudo fdisk -l sudo mkfs -t ext4 /dev/sda1
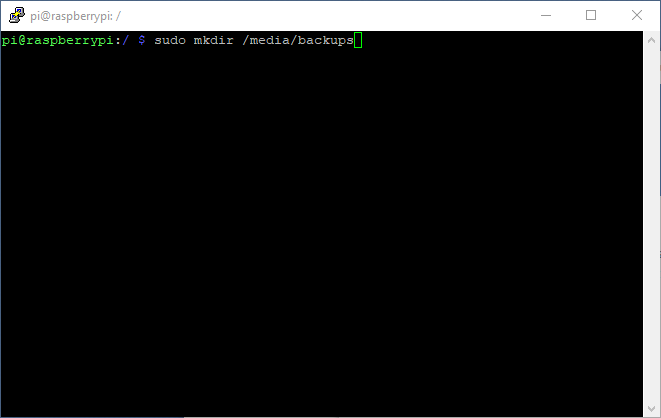
5. Now that we have formatted our drive, we need to ensure that this drive automatically mounts on boot. I will be mounting this to the /media/backups folder that I create, but you can put this wherever you’d like.
sudo mkdir /media/backups
6. The next step is to get the UUID of your external hard drive so that we can update the fstab file and mount the drive on boot. Run the command below and copy the UUID of your external hard drive. When copied, run the command below to update the fstab file.
sudo blkid sudo nano /etc/fstab
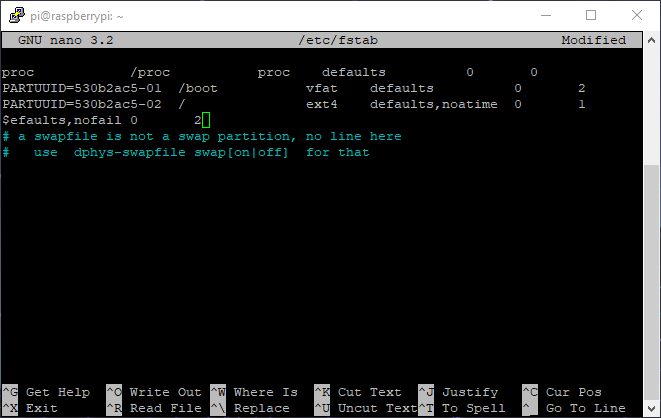
7. Enter in the line exactly as shown below and write out the file by pressing CTRL + O when complete. NOTE: You must “tab” between each block of text (each space below). It is also important to note that the “nofail” parameter allows you to boot the Raspberry Pi without the external hard drive attached – if this doesn’t exist, your Raspberry Pi will throw an error when the external hard drive is not connected and won’t boot.
UUID=[the UUID of your external hard drive] /media/backups ext4 defaults,nofail 0 2
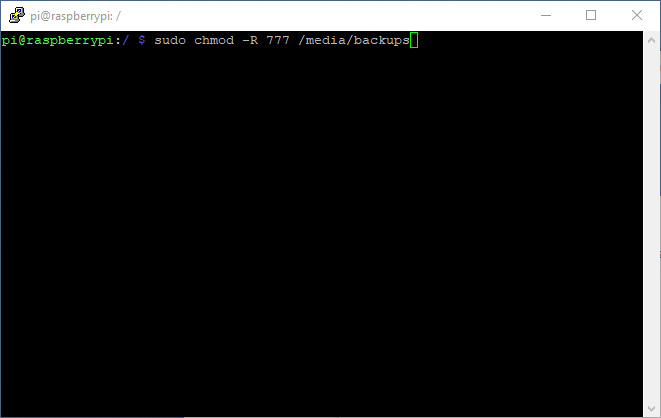
8. Give everyone read/write access to the newly created folder where your drive will be mapped. When done, reboot your Raspberry Pi and ensure that the drive mapped properly.
sudo chmod -R 777 /media/backups sudo reboot now
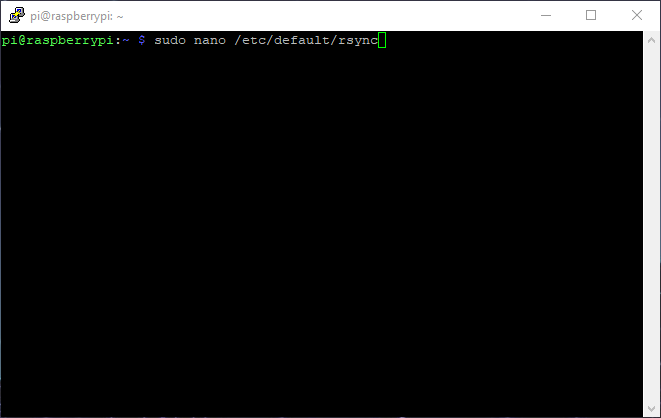
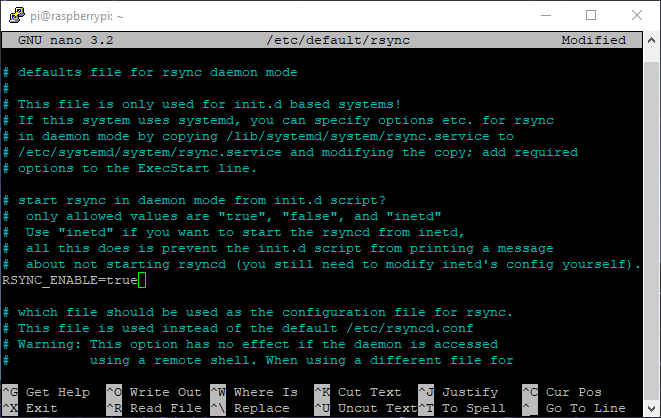
9. The drive is now formatted and mounted. The next steps are to setup the Rsync server. Run the command below to edit the Rsync server file.
sudo nano /etc/default/rsync
10. Change “RSYNC_ENABLE” from “false” to “true”.
11. Navigate to your “pi” users home directory and create an “rsyncd.conf” file. NOTE: since we will be utilizing SSH for our Rsync backup, the setup is different than a traditional Rsync server.
cd /home/pi sudo nano rsyncd.conf
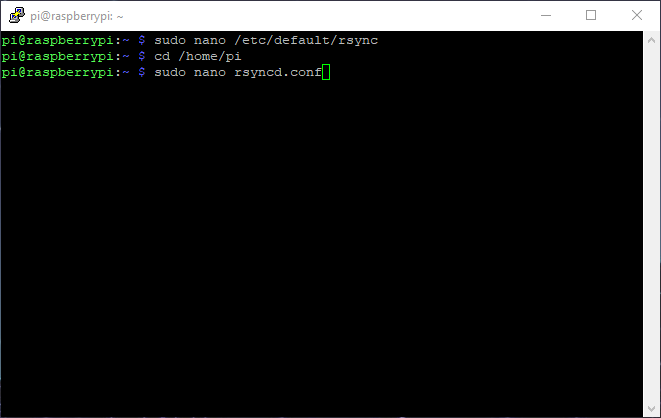
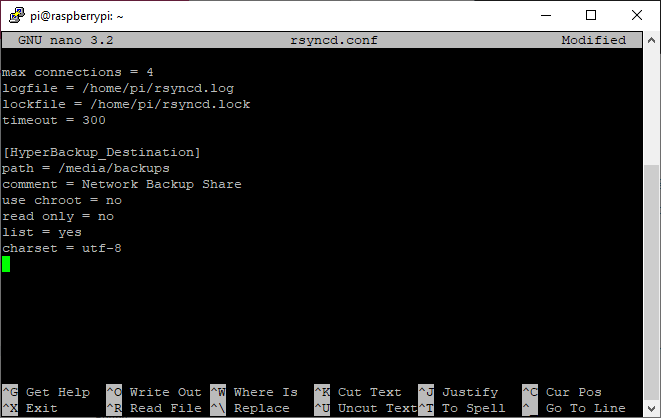
12. In your newly created file, enter the text below and save by pressing CTRL + O.
max connections = 4 logfile = /home/pi/rsyncd.log lockfile = /home/pi/rsyncd.lock timeout = 300
[HyperBackup_Destination]
path = /media/backups
comment = Network Backup Share
use chroot = no
read only = no
list = yes
charset = utf-8
13. Enable the Rsync service. This step may not be necessary, but it doesn’t hurt to run. Reboot the system.
sudo systemctl enable rsync sudo reboot now
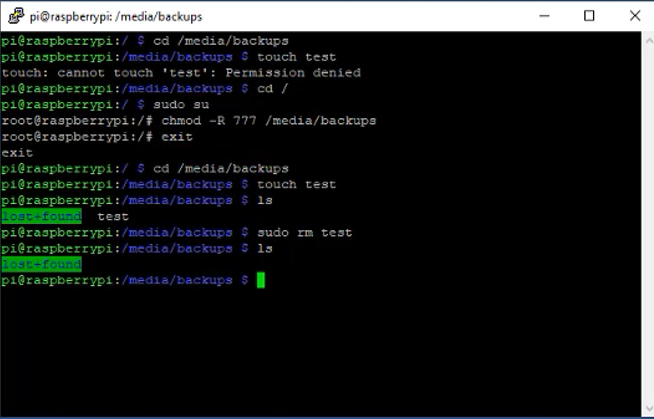
MOUNTED DRIVE TEST
Before proceeding, ensure that you are able to create a file in the newly created folder that is mapped to your external hard drive.
cd /media/backups touch test
If you get a permission denied error, you need to grant users read/write permissions to the directory using root.
sudo su chmod -R 777 /media/backups exit
Ensure that you can now create a file.
cd /media/backups touch test
If you can, remove the newly created file.
sudo rm test
At this point, you can connect to Hyper Backup and configure the Rsync backup job. We will be connecting to our Raspberry Pi using the default username (pi) and password (raspberry – this should be changed). This will allow the backup job to utilize SSH which will keep all traffic encrypted. You will also be able to setup client-side encryption in later steps if you’d like to encrypt the backup files.
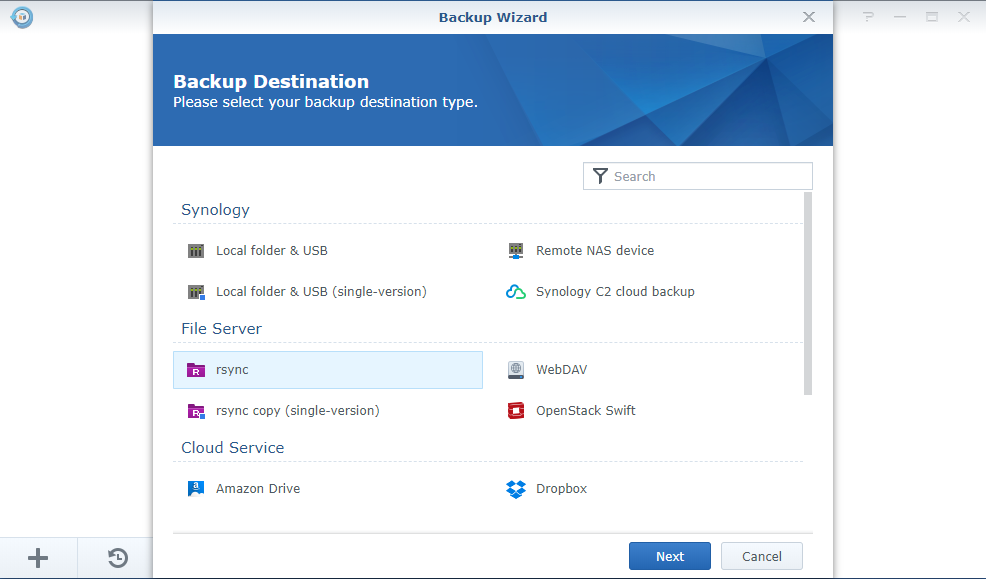
15. Open Hyper Backup and Create a new backup job. Select Rsync as the destination.
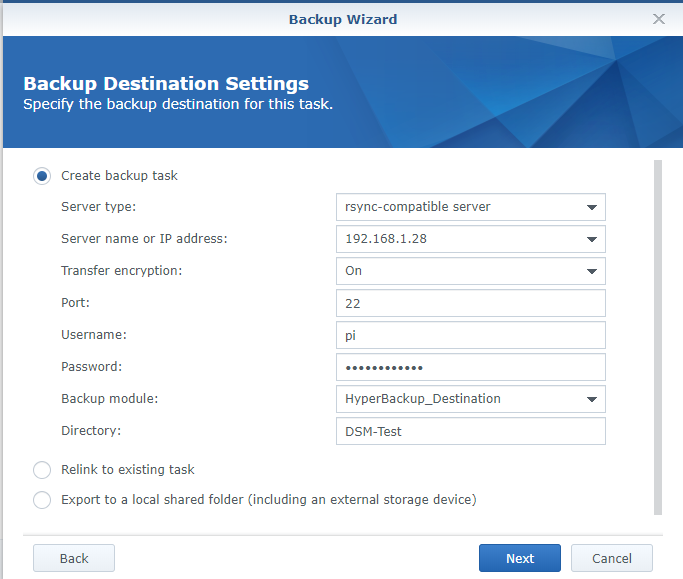
16. At the next step, configure the backup job as shown below. NOTE: you will need to substitute your Raspberry Pi’s IP address or hostname (default hostname is raspberrypi). The “Directory” text field is your backup’s file name.
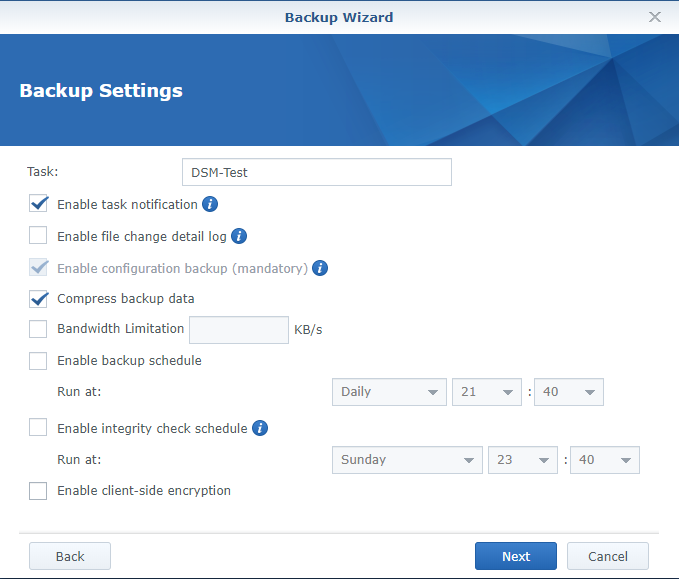
17. Configure the folders, applications, backup settings and proceed. NOTE: if you want to enable client-side encryption, you can select it here. On my production server, I use this option as my Raspberry Pi is setup as an offsite backup and I want to ensure the data is protected. It is important to note that if you lose this password or encryption key, you will be unable to restore your data. This step is optional.
The Rsync server setup process is now complete. At this time, if you plan on using your Raspberry Pi as an onsite backup, you don’t have to go any further. If you intend on using your Raspberry Pi as an offsite backup, the next steps will walk you through the process of setting up your Raspberry Pi to automatically connect to your OpenVPN server on boot. This allows you to put this device at a friend or family members house and ensure that it boots up and connects back to your home network without any user interaction.
Configure your Raspberry Pi to Automatically Connect to OpenVPN on Boot!
As stated earlier, I decided to setup my Raspberry Pi to automatically connect to my OpenVPN server so that I can have a family member turn on the Raspberry Pi and ensure it has an ethernet cable plugged in. I believed that if the process was more complex than that, I wouldn’t use it very often as I am using this as an offline backup. I am using the VPN Server application on my Synology NAS but any OpenVPN server will work. Just ensure that you have your “.ovpn” configuration file.
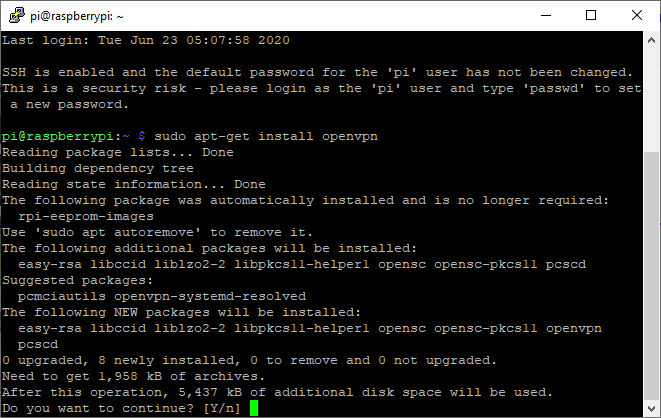
1. Install OpenVPN on your Raspberry Pi.
sudo apt-get install openvpn
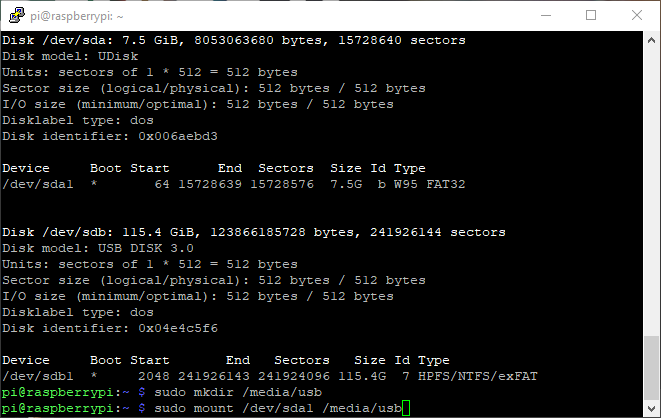
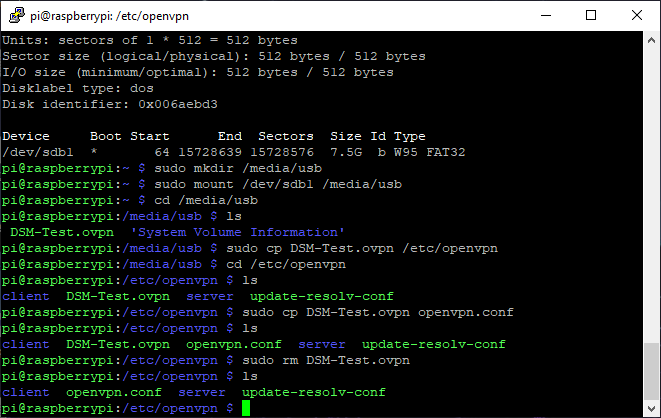
2. To transfer my “.ovpn” file to my Raspberry Pi, I inserted an external USB drive, mounted the drive to a local folder and copied the files to the OpenVPN directory. Follow the instructions below:
sudo fdisk -l
NOTE: If you don’t have an OpenVPN file already configured, you can use this template. Ensure that you add your DDNS name to the top and the correct certificate info at the bottom.
dev tun tls-client remote [YOUR DDNS NAME] 1194 push "redirect-gateway def1" pull proto udp script-security 2 comp-lzo reneg-sec 0 cipher AES-256-CBC auth SHA256 auth-user-pass .secrets keepalive 10 120 <ca> -----BEGIN CERTIFICATE----- [YOUR CERT] -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- [YOUR CERT] -----END CERTIFICATE----- </ca>
3. Make a new directory and mount the USB drive to that directory.
sudo mkdir /media/usb sudo mount /dev/sdb1 /media/usb
4. Navigate to the mounted folder.
cd /media/usb
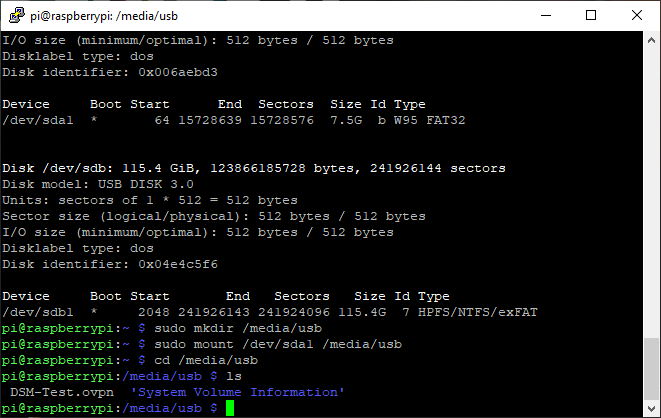
5. Copy the “.ovpn” file to your “/etc/ovpn” folder.
sudo cp DSM-TEST.ovpn /etc/openvpn
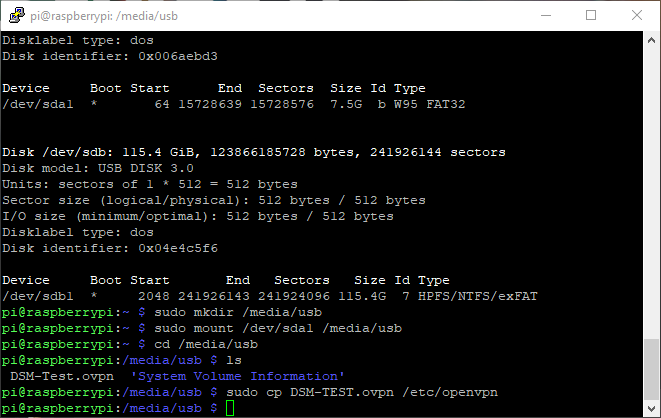
6. Navigate to the “openvpn” folder, copy the file to the same directory and ensure that the name is exactly this: “openvpn.conf”. When completed, remove the old file.
cd /etc/openvpn sudo cp DSM-Test.ovpn openvpn.conf sudo rm DSM-Test.ovpn
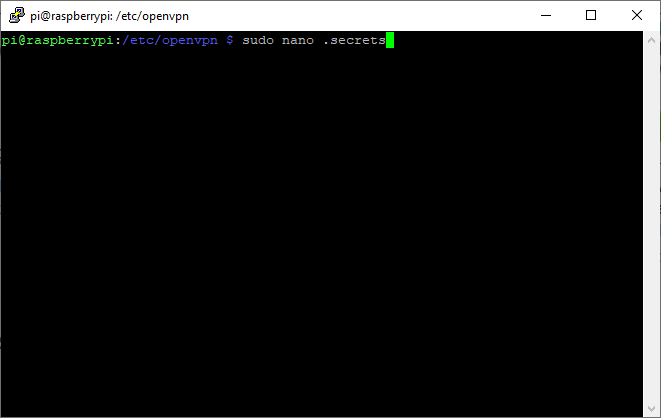
7. Next, we need to create a “.secrets” file.
sudo nano .secrets
8. Enter in the username and password of your VPN user. Save the file by pressing CTRL + O.
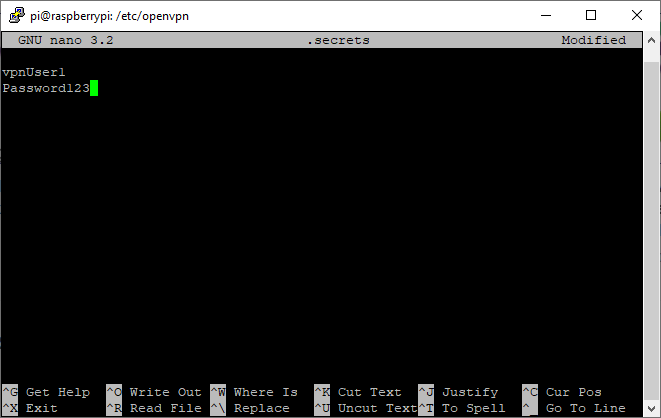
9. Change the permissions on the newly created “.secrets” file.
sudo chmod 400 .secrets
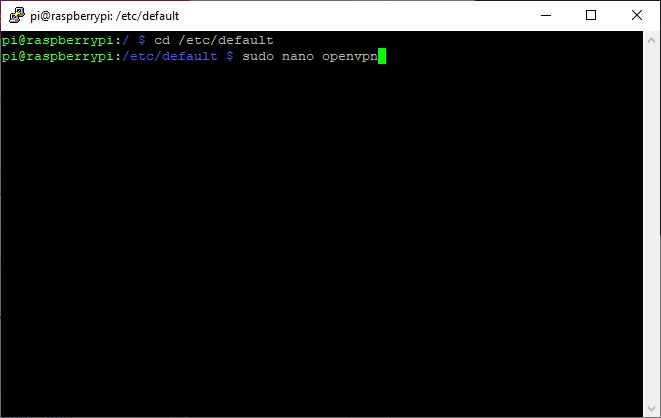
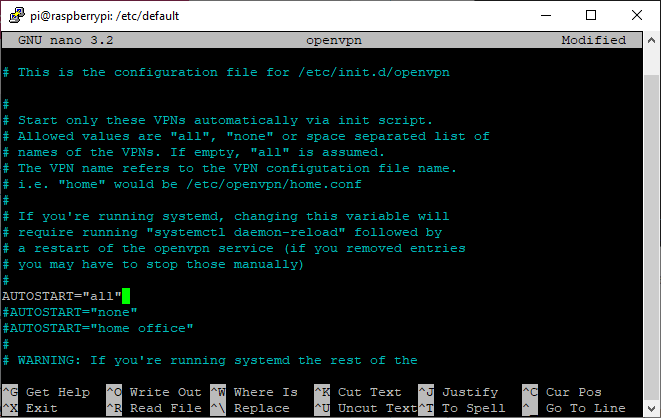
10. Navigate to the “/etc/default” directory and edit the “openvpn” file.
cd /etc/default sudo nano openvpn
11. Uncomment “autostart=”all” and save the file by pressing CTRL + O.
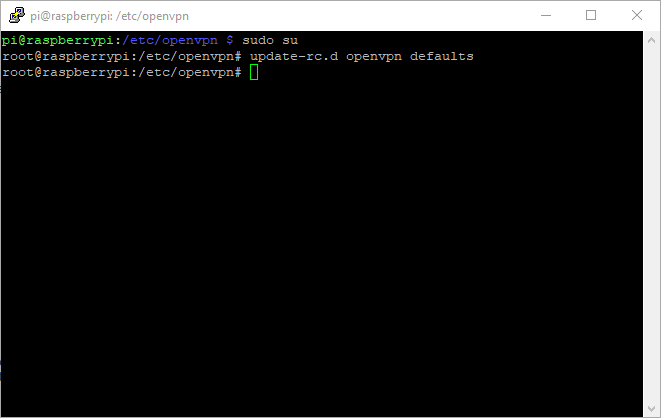
11. Update the OpenVPN service so that it starts by default. Ensure that you are root before running this command.
sudo su update-rc.d openvpn defaults
11. Reboot your Raspberry Pi.
sudo reboot now
The Raspberry Pi should now boot up and automatically connect to your VPN! When you test your VPN, you will need to be connected to an external network. If you have a hotspot on your cell phone, this is the “easiest” way to test.
VERY IMPORTANT SETUP INFORMATION
Your home network and VPN network will be on different subnets which means that devices will only be able to talk to the machines on their subnet. In order to have each subnet talk to each other (in my case, 192.168.1.X and 10.5.0.X), a static route will need to be configured in your router. I cannot go over the setup steps for this as each router is different, but below is a screenshot of the static route that I configured.

SETUP NOTES
- The combination of the “Destination IP Address” and “IP Subnet Mask” is what will determine what addresses can speak to the “Gateway IP Address”. This entry should be listed as your VPN’s dynamic IP range (in my case, 10.5.0.0).
- The “Gateway IP Address” is listed as your Synology NAS if you are using the VPN Server application.
- After you configure your Static Route, you must restart your Synology NAS so that it picks up the newly added static route.
- You will notice that you cannot ping from subnet A (192.168.1.0/24) to subnet B (10.5.0.0/24) without creating a static route. This static route is what will allow you to setup your Raspberry Pi’s static VPN IP address and connect to it.
Conclusion – Backup a Synology NAS to a Raspberry Pi
This tutorial showed how to backup a Synology NAS to a Raspberry Pi using Hyper Backup. If you care about your data, backups are integral. However, when you’re trying to backup a NAS, you generally have to pick and choose what you want to backup as NAS units normally have many terabytes of data stored. The process above was my solution to backing up “important” data, but not important enough data that I wanted to pay for cloud storage.
For my important data that I can’t lose, I use Backblaze B2 and I’m happy to pay the monthly costs. However, for my media, I couldn’t justify paying $240 a year for 4TB of storage that rarely changes and isn’t super important, which is why I’m very proud of this solution. For ~$130, I have an off-site backup solution that works just as well as some cloud offerings and can be restored significantly quicker than any cloud storage provider offers. This won’t be the best solution for everyone, but it’s a relatively easy way to backup a Synology NAS to a Raspberry Pi.
If you made it this far, thanks a lot for checking out the tutorial! If you have any questions, please leave them in the comments and I will do my best to answer them!